What is DevOps Monitoring?
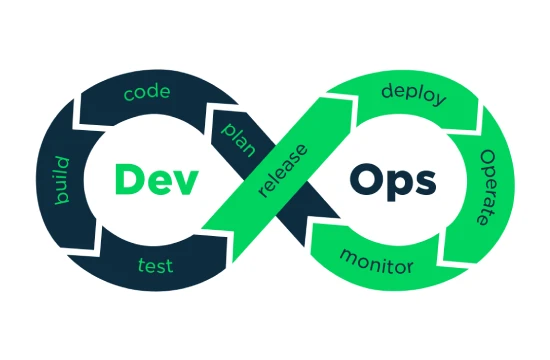
DevOps monitoring is a critical practice within the DevOps methodology, which emphasizes collaboration between development and operations teams to streamline software delivery and improve system reliability. At its core, DevOps monitoring involves the continuous observation, analysis, and management of applications, infrastructure, and processes throughout the software development lifecycle (SDLC). By providing real-time insights into system performance, DevOps monitoring ensures that teams can identify issues, optimize resources, and maintain high-quality software deployments.
In traditional software development models, monitoring was often an afterthought, relegated to the operations team once the application was deployed. However, the DevOps approach integrates monitoring into every stage of the SDLC, from coding and testing to deployment and production. This shift enables teams to detect and resolve problems early, reducing downtime and improving user satisfaction. DevOps monitoring encompasses a wide range of activities, including tracking application performance, monitoring server health, analyzing logs, and measuring key performance indicators (KPIs) such as response time, error rates, and resource utilization.
One of the defining features of DevOps monitoring is its reliance on automation and advanced tools. Tools like Prometheus, Grafana, Nagios, and Datadog allow teams to collect and visualize data in real time, making it easier to spot anomalies and trends. These tools integrate seamlessly with continuous integration and continuous deployment (CI/CD) pipelines, enabling automated testing, deployment, and monitoring workflows. For example, if a new code deployment causes a spike in error rates, DevOps monitoring tools can trigger alerts, allowing teams to roll back the deployment or address the issue immediately.
DevOps monitoring also emphasizes a proactive rather than reactive approach. Instead of waiting for failures to occur, teams use monitoring data to anticipate potential issues and optimize performance. This might involve setting up thresholds for CPU usage, memory consumption, or latency, and receiving notifications when these thresholds are breached. By combining monitoring with observability—gathering detailed insights into system behavior—teams gain a deeper understanding of how their applications and infrastructure interact, leading to faster troubleshooting and more resilient systems.
Another key aspect of DevOps monitoring is its focus on collaboration. Developers, operations staff, and other stakeholders share access to monitoring dashboards and metrics, fostering a culture of transparency and shared responsibility. This collaborative approach aligns with the broader goals of DevOps, breaking down silos and ensuring that everyone works toward the same objectives: delivering reliable, high-performing software to end users.
Key Components of DevOps Monitoring
DevOps monitoring is a multifaceted practice that relies on several key components to ensure the smooth operation of software systems and infrastructure. These components work together to provide real-time visibility, enable proactive issue resolution, and support the continuous improvement of development and operations workflows. Understanding these elements is essential for implementing an effective DevOps monitoring strategy that aligns with organizational goals and enhances software delivery.
- Metrics Collection and Analysis
Metrics are the foundation of DevOps monitoring. They provide quantitative data about system performance, application health, and user experience. Common metrics include response times, error rates, CPU and memory usage, network latency, and throughput. Tools like Prometheus or New Relic collect these metrics from applications, servers, and databases, allowing teams to analyze trends and establish performance baselines. By setting thresholds for acceptable metric values, teams can receive alerts when anomalies occur, enabling rapid response to potential issues. - Log Management
Logs are detailed records of events and activities within an application or system. DevOps monitoring relies on centralized log management systems, such as ELK Stack (Elasticsearch, Logstash, Kibana) or Splunk, to aggregate and analyze logs from various sources. These logs provide context for troubleshooting issues, such as identifying the root cause of an error or tracking user interactions. Effective log management involves filtering, searching, and visualizing log data to uncover patterns and insights that improve system reliability. - Real-Time Dashboards and Visualization
Visualization tools like Grafana or Datadog dashboards are integral to DevOps monitoring, offering a real-time view of system health and performance. These dashboards display metrics, logs, and alerts in an accessible format, allowing teams to monitor multiple components simultaneously. Customizable dashboards enable stakeholders to focus on the most relevant data for their roles, fostering collaboration and quick decision-making. Real-time visualization ensures that teams can detect and address issues as they arise, minimizing downtime and maintaining service quality. - Alerts and Notifications
Alerts are a proactive component of DevOps monitoring, designed to notify teams when predefined thresholds or conditions are met. For example, an alert might trigger if server CPU usage exceeds 90% or if an application experiences a sudden spike in errors. Tools like PagerDuty or Opsgenie integrate with monitoring systems to send notifications via email, SMS, or chat platforms like Slack. Effective alerting ensures that the right team members are informed promptly, enabling swift resolution of issues before they impact users. - Integration with CI/CD Pipelines
DevOps monitoring is tightly integrated with continuous integration and continuous deployment (CI/CD) pipelines. Tools like Jenkins, GitLab CI/CD, or CircleCI incorporate monitoring at every stage of the pipeline, from code commits to production deployments. This integration allows teams to test and monitor code changes in real time, ensuring that only stable, high-quality updates are deployed. Automated rollback mechanisms, triggered by monitoring alerts, further enhance the reliability of CI/CD workflows.
Benefits of DevOps Monitoring for Teams
DevOps monitoring is a multifaceted practice that relies on several key components to ensure the smooth operation of software systems and infrastructure. These components work together to provide real-time visibility, enable proactive issue resolution, and support the continuous improvement of development and operations workflows. Understanding these elements is essential for implementing an effective DevOps monitoring strategy that aligns with organizational goals and enhances software delivery.
- Metrics Collection and Analysis
Metrics are the foundation of DevOps monitoring. They provide quantitative data about system performance, application health, and user experience. Common metrics include response times, error rates, CPU and memory usage, network latency, and throughput. Tools like Prometheus or New Relic collect these metrics from applications, servers, and databases, allowing teams to analyze trends and establish performance baselines. By setting thresholds for acceptable metric values, teams can receive alerts when anomalies occur, enabling rapid response to potential issues. - Log Management
Logs are detailed records of events and activities within an application or system. DevOps monitoring relies on centralized log management systems, such as ELK Stack (Elasticsearch, Logstash, Kibana) or Splunk, to aggregate and analyze logs from various sources. These logs provide context for troubleshooting issues, such as identifying the root cause of an error or tracking user interactions. Effective log management involves filtering, searching, and visualizing log data to uncover patterns and insights that improve system reliability. - Real-Time Dashboards and Visualization
Visualization tools like Grafana or Datadog dashboards are integral to DevOps monitoring, offering a real-time view of system health and performance. These dashboards display metrics, logs, and alerts in an accessible format, allowing teams to monitor multiple components simultaneously. Customizable dashboards enable stakeholders to focus on the most relevant data for their roles, fostering collaboration and quick decision-making. Real-time visualization ensures that teams can detect and address issues as they arise, minimizing downtime and maintaining service quality. - Alerts and Notifications
Alerts are a proactive component of DevOps monitoring, designed to notify teams when predefined thresholds or conditions are met. For example, an alert might trigger if server CPU usage exceeds 90% or if an application experiences a sudden spike in errors. Tools like PagerDuty or Opsgenie integrate with monitoring systems to send notifications via email, SMS, or chat platforms like Slack. Effective alerting ensures that the right team members are informed promptly, enabling swift resolution of issues before they impact users. - Integration with CI/CD Pipelines
DevOps monitoring is tightly integrated with continuous integration and continuous deployment (CI/CD) pipelines. Tools like Jenkins, GitLab CI/CD, or CircleCI incorporate monitoring at every stage of the pipeline, from code commits to production deployments. This integration allows teams to test and monitor code changes in real time, ensuring that only stable, high-quality updates are deployed. Automated rollback mechanisms, triggered by monitoring alerts, further enhance the reliability of CI/CD workflows.
How to Set Up DevOps Monitoring
Setting up DevOps monitoring is a strategic process that enables teams to gain visibility into their systems, detect issues early, and optimize software delivery. While the specifics may vary depending on an organization’s tools, infrastructure, and goals, the following steps provide a comprehensive guide to establishing an effective DevOps monitoring framework. By following these steps, teams can ensure they have the tools, processes, and mindset needed to monitor applications and infrastructure successfully.
- Define Monitoring Goals and Metrics
The first step in setting up DevOps monitoring is to define clear objectives and identify the key performance indicators (KPIs) that matter most to your team. These goals might include minimizing downtime, reducing latency, or improving deployment frequency. Based on these objectives, select relevant metrics to track, such as response time, error rates, CPU and memory usage, or user satisfaction scores. Establishing these metrics upfront ensures that your monitoring efforts align with business and technical priorities. - Choose the Right Monitoring Tools
Selecting appropriate tools is critical for effective DevOps monitoring. Popular options include Prometheus for metrics collection, Grafana for visualization, ELK Stack for log management, and Datadog or New Relic for end-to-end monitoring. Consider factors like scalability, ease of integration, and community support when choosing tools. Many teams use a combination of tools to cover different aspects of monitoring, such as application performance, infrastructure health, and user experience. Ensure the tools you select integrate well with your existing CI/CD pipeline and infrastructure. - Set Up Data Collection and Instrumentation
Once tools are selected, configure them to collect data from your applications and infrastructure. This involves instrumenting your code with monitoring agents or libraries (e.g., adding Prometheus exporters) and setting up monitoring for servers, databases, and network components. Ensure that logs, metrics, and traces are collected consistently across all environments—development, staging, and production. Centralized data collection enables teams to analyze system behavior and detect anomalies effectively. - Create Dashboards and Alerts
With data collection in place, set up real-time dashboards to visualize key metrics and logs. Tools like Grafana allow you to create custom dashboards that display the most critical information for your team, such as application uptime or resource utilization. Next, configure alerts based on predefined thresholds—for example, notifying the team if error rates exceed 5% or if server memory usage surpasses 80%. Use notification platforms like Slack, PagerDuty, or email to ensure alerts reach the right team members promptly. - Integrate Monitoring with CI/CD Pipelines
To fully embed monitoring into your DevOps workflow, integrate it with your CI/CD pipeline. Tools like Jenkins or GitLab CI/CD can incorporate monitoring checks at each stage, such as running tests or validating performance metrics before deployment. Automated rollback mechanisms can also be implemented, allowing the pipeline to revert changes if monitoring detects issues post-deployment. This integration ensures that monitoring is a continuous part of the development and deployment process. - Test, Iterate, and Train the Team
After setting up monitoring, test the system to ensure it works as expected. Simulate failures or performance issues to verify that alerts trigger correctly and dashboards provide actionable insights. Continuously iterate on your setup by refining metrics, adjusting thresholds, and adding new monitoring capabilities as needed. Finally, train team members on how to use the tools, interpret data, and respond to alerts, fostering a culture of shared responsibility and proactive monitoring.