What is a Botnet?
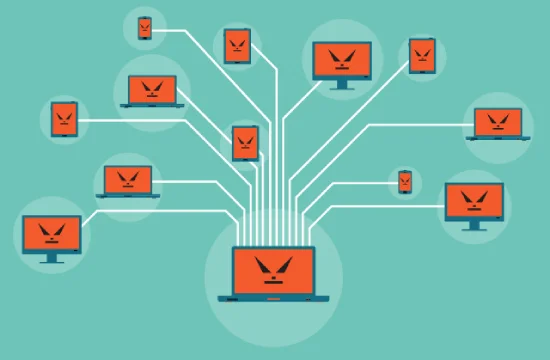
A botnet is a network of compromised computers, devices, or servers that are infected with malware and controlled remotely by a cybercriminal, often referred to as a bot herder or botmaster. The term "botnet" is derived from "robot" and "network," signifying an automated system of interconnected devices that execute commands without the owners’ knowledge. These compromised devices, also called bots or zombies, are typically used for malicious activities, including distributed denial-of-service (DDoS) attacks, spamming, data theft, and financial fraud.
Botnets function by spreading malware that allows attackers to take control of multiple devices. This malware is often delivered through phishing emails, malicious downloads, or vulnerabilities in software and operating systems. Once a device is infected, it secretly connects to a command and control (C2) server, which issues instructions to all infected devices within the botnet. The C2 infrastructure enables the botmaster to manipulate thousands or even millions of compromised devices simultaneously, making botnets one of the most powerful tools in cybercrime.
One of the reasons botnets are so dangerous is their ability to operate stealthily. Most infected users remain unaware that their device is compromised, as botnet malware is designed to run in the background with minimal impact on system performance. This allows cybercriminals to maintain control over a large number of infected devices for extended periods without detection. Additionally, botnets often utilize decentralized architectures, such as peer-to-peer (P2P) networks, making them more resilient to takedown efforts by law enforcement and cybersecurity professionals.
Botnets have been responsible for some of the most devastating cyberattacks in history. Notable examples include the Mirai botnet, which targeted IoT devices and launched massive DDoS attacks, and the Zeus botnet, which was used for banking fraud and credential theft. As botnet technology evolves, cybercriminals continue to find new ways to exploit connected devices, particularly with the rise of the Internet of Things (IoT).
Preventing botnet infections requires a combination of cybersecurity best practices, including regular software updates, strong password policies, network monitoring, and advanced threat detection tools. Organizations and individuals should remain vigilant against phishing scams and suspicious downloads, as these are common infection vectors. By understanding how botnets operate and taking proactive security measures, users can reduce their risk of falling victim to these large-scale cyber threats.
Types of Botnets
Botnets come in various forms, each designed to carry out specific cybercriminal activities. While all botnets share the common characteristic of hijacking devices for malicious purposes, their structure and method of control can differ significantly. Understanding the different types of botnets helps cybersecurity professionals and users recognize potential threats and implement effective defense strategies.
One of the most common types is centralized botnets, which rely on a command and control (C2) server to communicate with all infected devices. In this model, the botmaster sends instructions from a single control point, and all bots within the network follow the commands. This architecture allows for easy management of the botnet, but it also creates a single point of failure. If law enforcement or cybersecurity teams take down the C2 server, the entire botnet can be dismantled. Despite this vulnerability, centralized botnets remain widely used due to their simplicity and efficiency.
A more resilient variant is the peer-to-peer (P2P) botnet, which eliminates the need for a central command structure. Instead of relying on a single server, each infected device acts as both a client and a server, distributing control commands across the network. This decentralized approach makes P2P botnets much harder to take down, as there is no central hub to target. Cybercriminals favor P2P botnets because they are more resistant to law enforcement actions and cybersecurity interventions.
Another dangerous category is botnets designed specifically for distributed denial-of-service (DDoS) attacks. These botnets flood target websites or online services with massive amounts of traffic, overwhelming servers and causing disruptions. DDoS botnets are often rented out as part of “booter” or “stresser” services, allowing attackers to launch devastating attacks against businesses, governments, and individuals for a fee. Some of the most infamous DDoS botnets, such as Mirai, have leveraged insecure IoT devices to amplify their attacks.
Financial fraud botnets focus on stealing banking credentials, credit card information, and personal data. These botnets infect computers with keyloggers, form grabbers, and other spyware designed to capture sensitive user information. The Zeus botnet is a well-known example that compromised millions of devices worldwide to steal financial data. These botnets often use stealth techniques to avoid detection and can remain active for long periods.
As cybercriminal tactics evolve, botnets continue to adapt, targeting a growing range of devices, including smartphones, IoT gadgets, and cloud-based systems. Understanding the different types of botnets is crucial for developing robust cybersecurity measures to mitigate these threats.
How to Detect and Prevent Botnet Infections
Detecting and preventing botnet infections is critical for individuals and organizations to protect their devices and networks from cybercriminals. Since botnets operate stealthily, they can be challenging to identify, but certain signs and proactive security measures can help mitigate the risk of infection and minimize damage.
One of the most common indicators of a botnet infection is unusual network activity. If a device is suddenly transmitting large amounts of data without user intervention or is connecting to unknown IP addresses, it may be part of a botnet. Frequent system slowdowns, high CPU usage, or unresponsive applications can also be signs that malware is running in the background. Additionally, unexpected crashes, unauthorized processes in the task manager, or antivirus programs being disabled without user input may indicate that a botnet has taken control of the device.
Monitoring outbound traffic and scanning for irregular patterns is a crucial method for detecting botnets. Since infected devices communicate with a command and control (C2) server, analyzing network logs can reveal suspicious communication attempts. Many cybersecurity tools and intrusion detection systems (IDS) are designed to flag abnormal behavior, helping organizations identify potential infections before they cause significant harm.
Preventing botnet infections requires a combination of strong cybersecurity hygiene and advanced security solutions. Regularly updating software, operating systems, and firmware helps patch vulnerabilities that cybercriminals exploit to deploy botnet malware. Strong, unique passwords for all accounts and network-connected devices reduce the risk of unauthorized access. Enabling multi-factor authentication (MFA) further enhances security by adding an extra layer of protection against credential theft.
Installing and maintaining reputable antivirus and anti-malware software is another essential step in preventing botnet infections. These tools can detect and remove malicious software before it spreads and connects to a botnet. Additionally, using a firewall helps block unauthorized connections and prevents malware from communicating with C2 servers.
Educating users about phishing attacks is also crucial, as many botnets spread through malicious email attachments, fake software downloads, and deceptive links. Organizations should implement security awareness training to teach employees how to recognize and avoid phishing attempts.
For businesses and enterprises, network segmentation can limit the spread of an infection if a device is compromised. Isolating critical systems and restricting access to sensitive data can prevent a single botnet-infected device from compromising an entire network.
By combining proactive monitoring, robust security practices, and awareness training, individuals and organizations can significantly reduce the risk of botnet infections and protect their systems from cybercriminal threats